Crypto Exchange Development Company
IdeaSoft is top-notch provider of cryptocurrency exchange development services, delivering secure, high-performance trading platforms of any complexity.
Our cryptocurrency exchange development services
Leverage IdeaSoft team's in-depth knowledge and experience in our crypto exchange software development services. We bring a wealth of expertise to the table, ensuring that your trading solution stands out in the competitive market.
-
Centralized Crypto Exchange Development
-
Decentralized Crypto Exchange Development
-
Hybrid Crypto Exchange Development
-
Margin Trading Integration
-
DeFi Strategies Integration
-
OTC Functionality Development
Features of IdeaSoft Crypto Exchange Development Solutions
-
Liquidity Solutions
Tools and integrations to ensure seamless and efficient trading with minimal slippage. -
Custom Crypto Exchange Development
Fully tailored solutions to meet unique business requirements. -
DeFi Exchange Solutions
Specialized decentralized finance platforms for secure, peer-to-peer transactions. -
API Integration Services
Enable smooth integration of third-party services like payment gateways, market data, and analytics.
Talk to a Crypto Exchange Development Provider Today
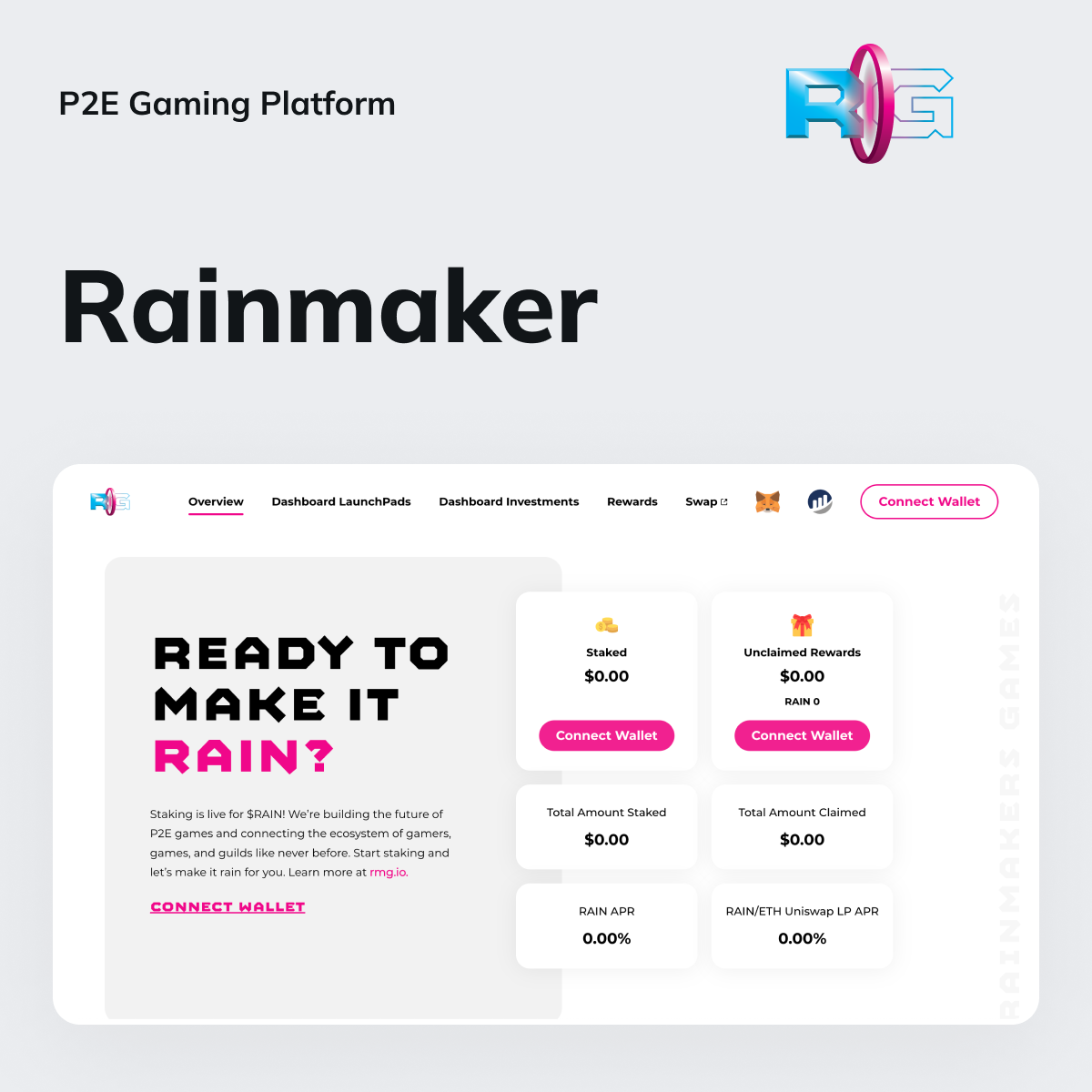
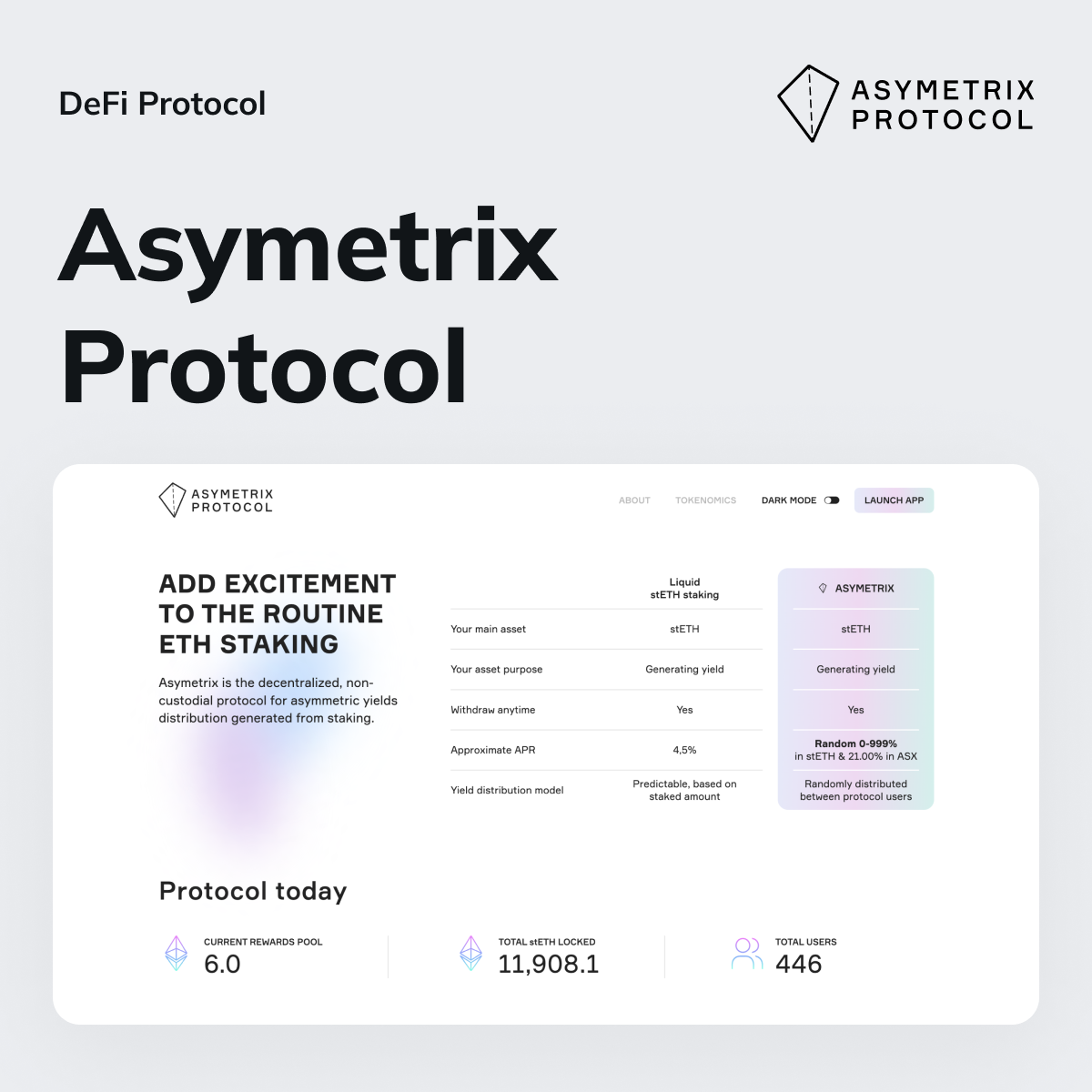
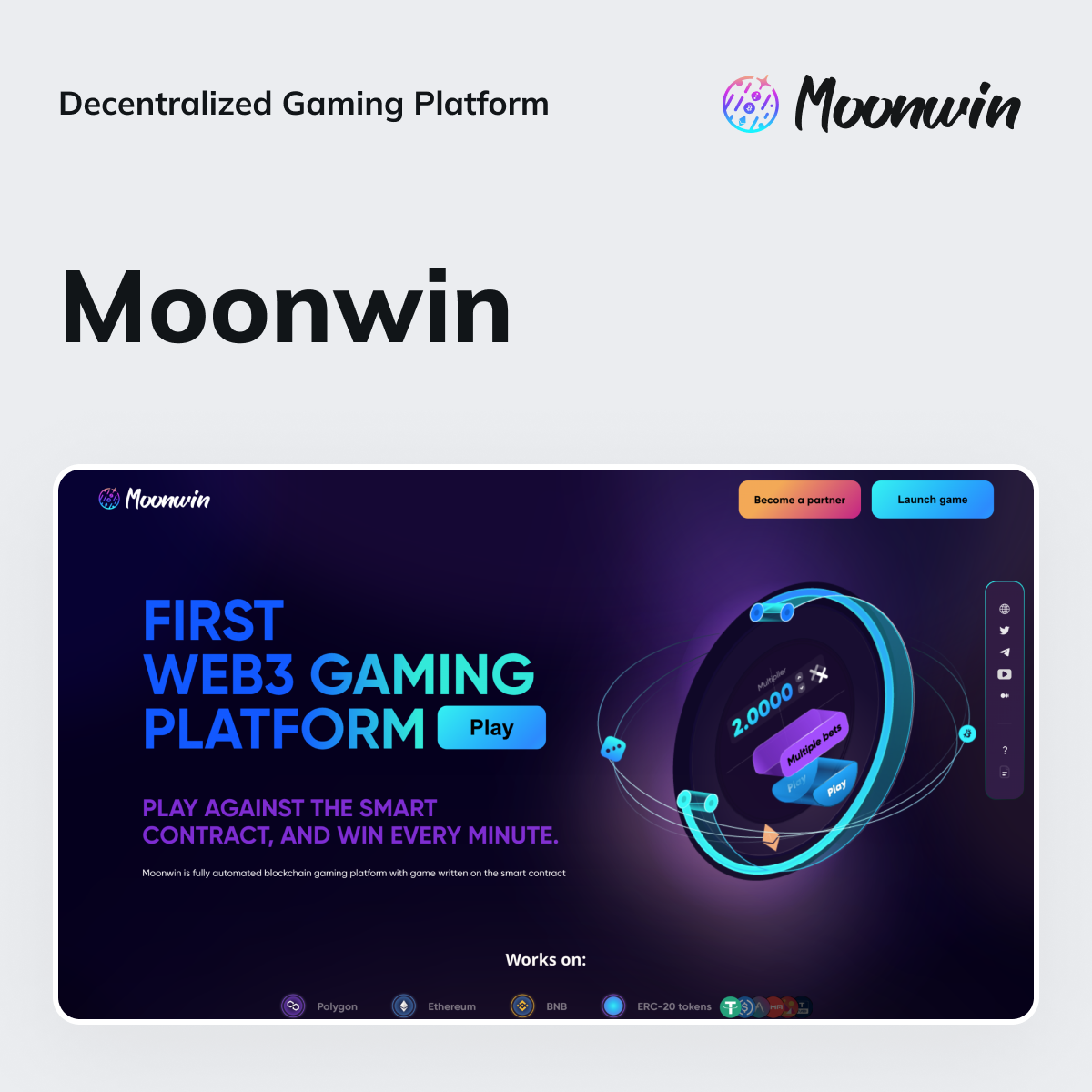
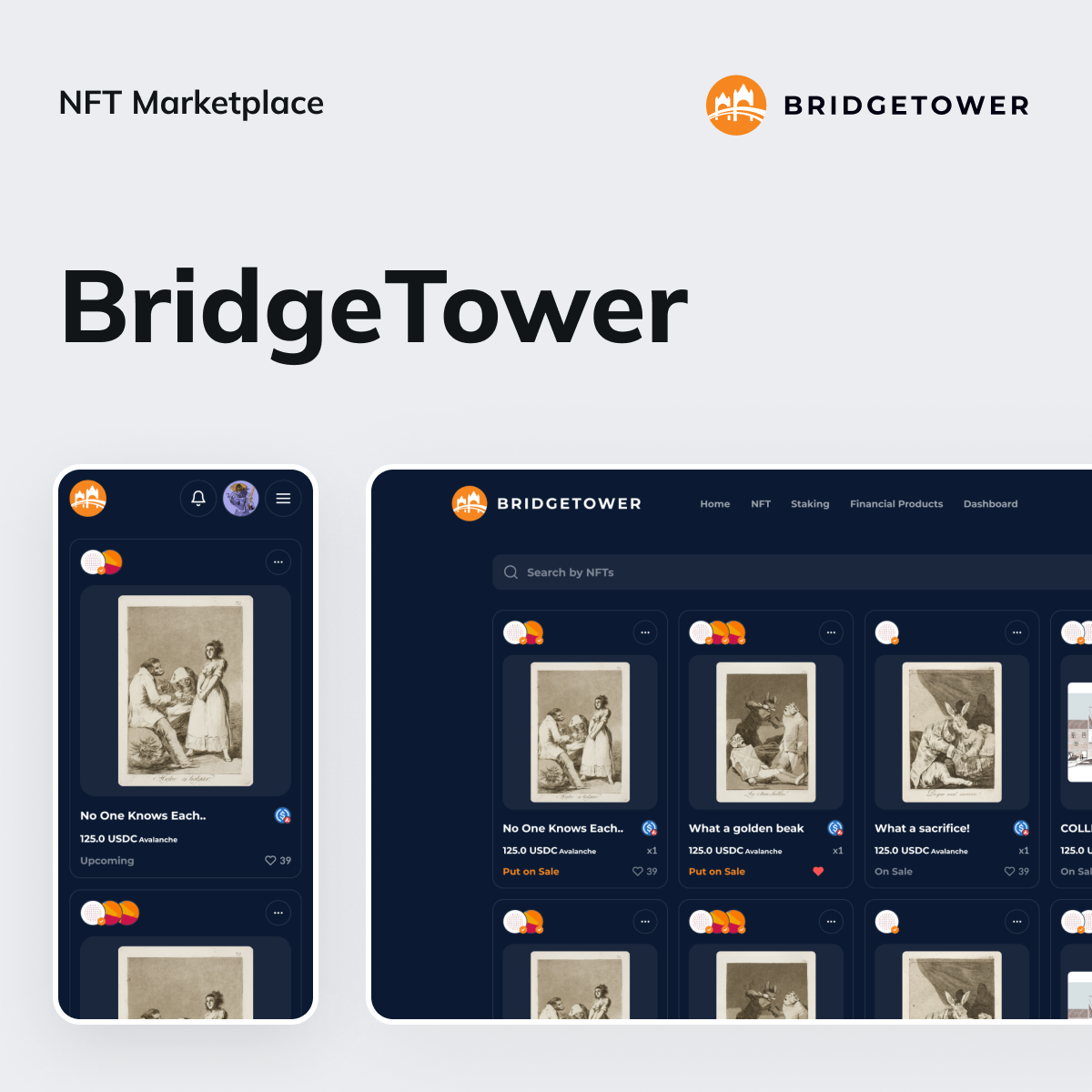
Our Case Studies
Our cryptocurrency exchange software development company excels in creating web3 architecture, applications, and custom blockchain solutions. Having effectively completed over 100 blockchain projects across different industries, our portfolio reflects our expertise and success in delivering innovative platforms and dApps.
Explore our collection of case studies to check how our solutions have positively impacted various sectors.
Why Choose IdeaSoft for Crypto Exchange Software Development?
-
Deep Blockchain Expertise
-
Strong Web3 UX Team
-
Compliance Expertise
-
Wide Tech Stack
-
Proven Track Record
-
Cost-effective Solutions
Let's Shape It with Our Crypto Exchange Developers
Our technologies for crypto exchange development
We stay up-to-date with the latest advancements in blockchain technology to ensure that your solutions are robust and forward-compatible.
Testimonials
Cryptocurrency Exchange Development Services
Frequently Asked Questions
-
How much does it cost to develop a cryptocurrency exchange software?The cost always varies based on features, complexity, and customization your solution will require. A basic exchange may start around $100,000, while more complex projects can range from $150,000 to $500,000 or more.
-
How long does it take to build and launch a crypto exchange software?The development time depends on features and customization. A basic exchange might take 3-6 months, while more complex projects could extend to 9-12 months.
-
How to choose the best crypto exchange development agency?Look for a cryptocurrency exchange development agency with a proven track record showcasing expertise in blockchain. Check the level of security measures the team applies and the ability to customize solutions. The best option is to develop with a team that can deliver end-to-end solutions without the need for third-party involvement or additional dev forces.
-
How can I build crypto exchange software?To build a solid DEX or CEX platform, partner with a reliable crypto exchange development company with expertise in blockchain technology. Ensure they offer end-to-end solutions, prioritize security, and have a transparent development process with clear deadlines and deliverables.